Singpass QR Login OIDC
integration | 2021-10-20
integration | 2021-10-20
Probably deprecated already
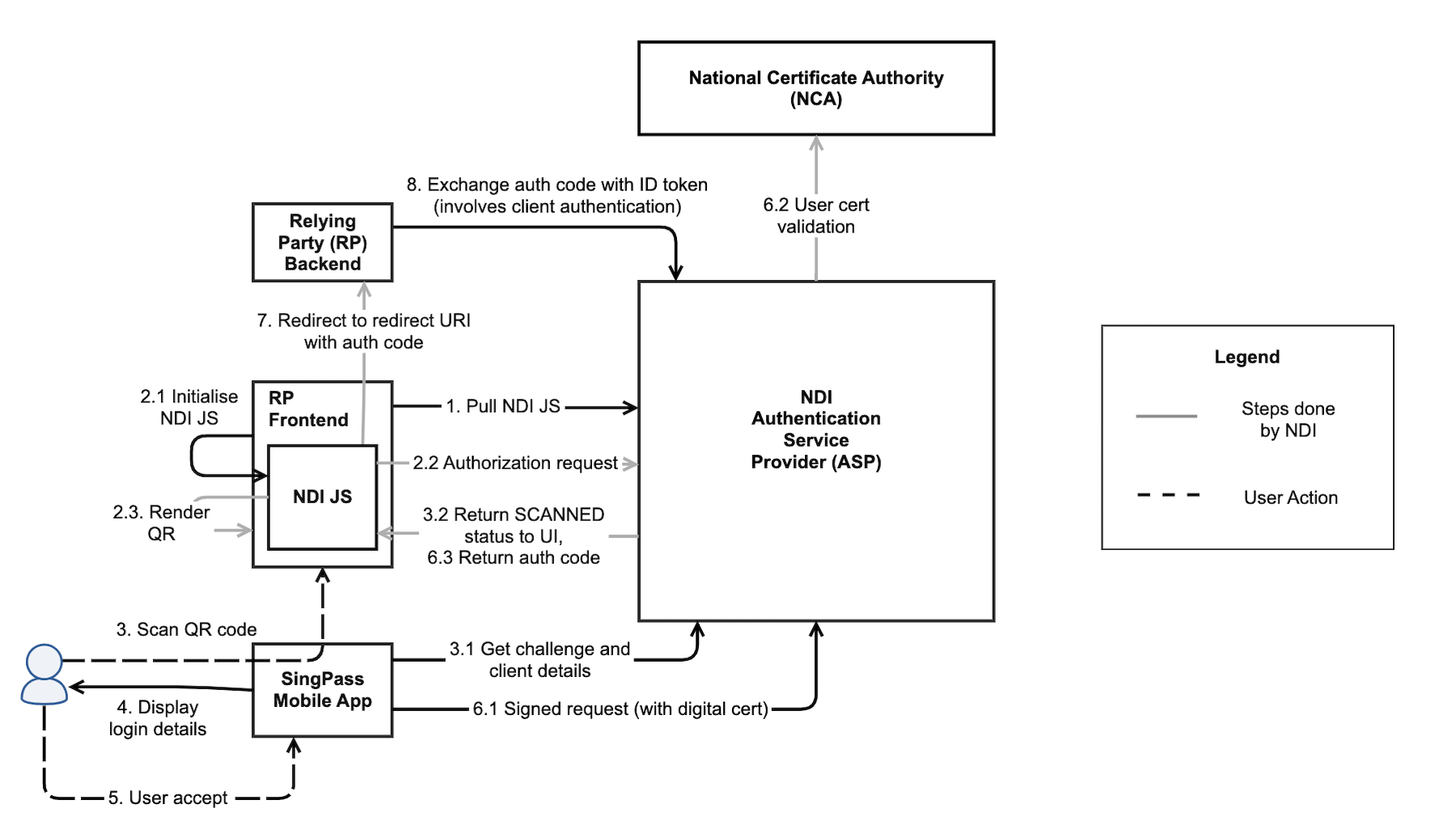
High level Frontend / Backend Login: Actor
OIDC authentication flow:
Go to Singpass API Onboarding, login with CorpPass
Then, the SingPass representative will engage you directly
(SingPass rep to provide) Onboarding form
After approval, (SingPass provide credential) you will obtain TestFlight accounts & client_id
The JSON Web Key Set (JWKS) endpoint is a read-only endpoint that returns the Identity Server"s public key set in the JWKS format. This contains the signing key(s) that the Relying Party (RP) uses to validate signatures from the Identity Server.
The signing JWK will be used to verify the client assertion JWT provided during /token request, thereby authenticating the client.
Steps to create:
Generate private and public key pairs:
encryption key, decryption key, signing key and verification key
openssl ecparam -name prime256v1 -genkey -noout -out singpass-decryption-key.pem
openssl ec -in singpass-decryption-key.pem -pubout -out singpass-encryption-key.pem
openssl ecparam -name prime256v1 -genkey -noout -out singpass-signing-key.pem
openssl ec -in singpass-signing-key.pem -pubout -out singpass-verification-key.pem
(Optional) Encrypt signing and decryption key
openssl ec -in singpass-decryption-key.pem -out singpass-decryption-key-encrypted.pem -aes256
openssl ec -in singpass-signing-key.pem -out singpass-signing-key-encrypted.pem -aes256
Using node-jose to create keystores, use asKey / asKeyStore - input, form and headers
Keystores consists of two public keys: enc (encryption-key) and sig (verification-key).
Build an APi and make sure it fulfilled the SingPass requirement to serve the jwks
Sample step / tutorial
NOTE
Setup TestFlight app (It doesnt work together with actual SingPass app, hence, you have to install at backup phone)
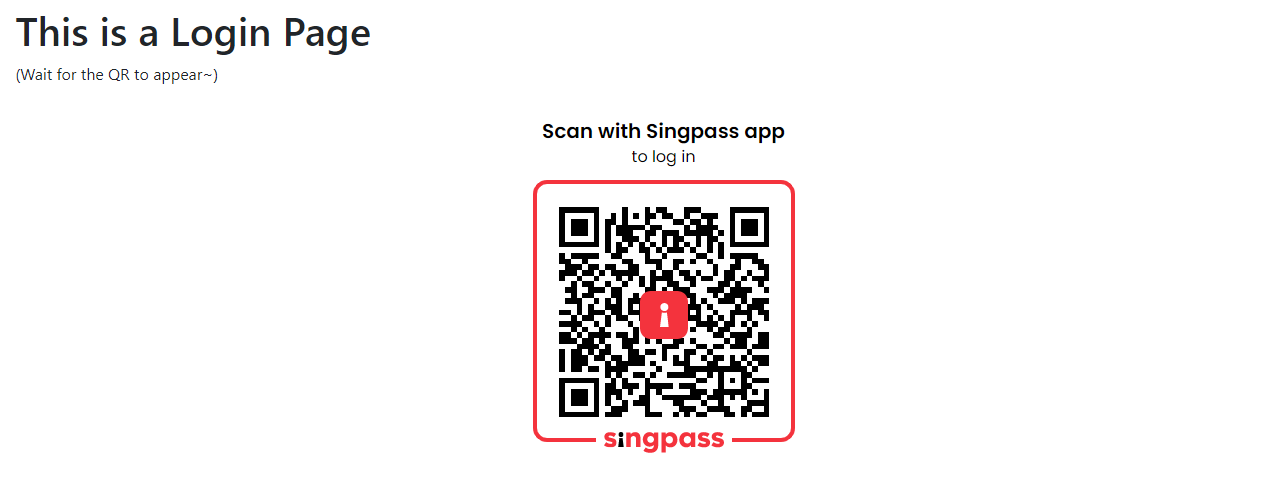
Follow the tutorial, specify clientId, redirectUri, scope, responseType
Then, you shall able to see the QR code and scan it using TestFlight
Lastly, it will callback to the redirect URL you provided
Sample step / tutorial
Build Client Assertion
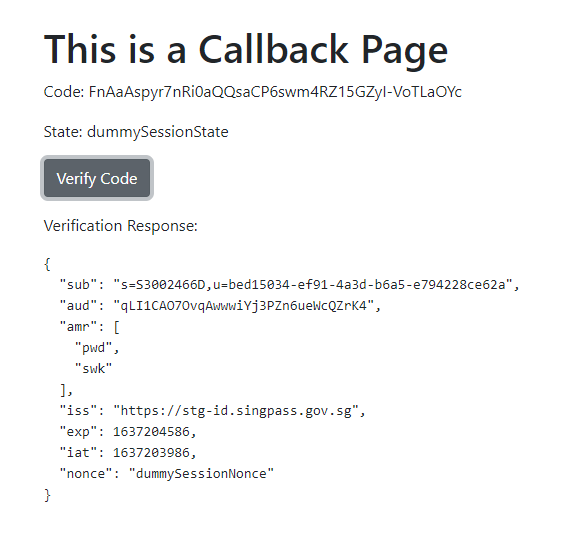
Build API to receive code and exchange for JWE (access_token, token_type and id_token)
Decrypt JWE and get a JWT token
Verify encrypted JWT token -Verify the decrypted JWT token with Singpass public key
Lastly, it will return payload with sub (IC id and U id)
Login Screen
Response / Verify Screen
How it works? Scenario below:
Demo: Check Demo Video
Demo in App